Cloud security: what you don't know will hurt you
- Data breaches
- Weak identity, credential and access management
- Insecure Application Programming Interfaces (APIs)
- System and application vulnerabilities
- Account hijacking
- Malicious insiders
- Advanced Persistent Threats (APTs)
- Data loss
- Insufficient due diligence
- Abuse and nefarious use of cloud services
- Denial of service
- Shared technology issues
On this page
Share this
Share this
More resources
Learn more about Pythian by reading the following blogs and articles.
Top 10 Benefits of Migrating Your Traditional Databases to Google Cloud


Top 10 Benefits of Migrating Your Traditional Databases to Google Cloud
Sep 11, 2024 1:34:27 PM
4
min read
Automated Database Backups for Cloud Spanner Using Terraform
Automated Database Backups for Cloud Spanner Using Terraform
Dec 17, 2021 12:00:00 AM
5
min read
Secure the Connection to Your VPC Network from Serverless Environments in Google Cloud
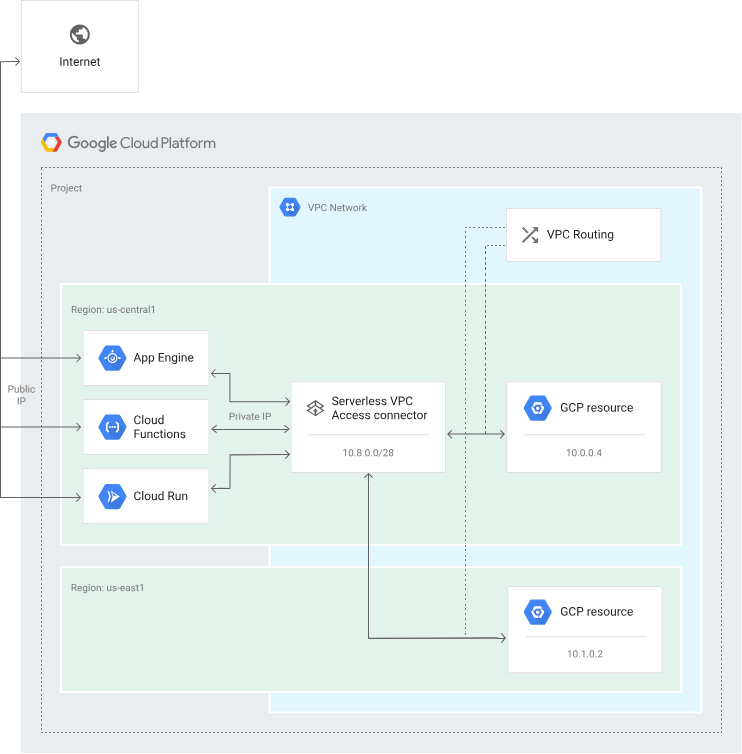
Secure the Connection to Your VPC Network from Serverless Environments in Google Cloud
Jan 12, 2024 1:16:55 PM
5
min read
Ready to unlock value from your data?
With Pythian, you can accomplish your data transformation goals and more.
