What is Oracle Data Safe and Why Should You Use It ?
Data Safe is an Oracle Cloud Infrastructure (OCI) security service that provides a set of features to protect sensitive and regulated data in Oracle databases, for both Standard and Enterprise Editions, since version 11.2.0.4.
OCI can assess your security configuration at the database level providing best practices recommendations, similar to the tool DBSAT (Database Security Assessment Tool), but Data Safe also provides features like Data Masking (without needing to have extra License) and Auditing–all easily configured in the OCI console. It can also be scheduled to automatically run periodically, you can set baselines, compare reports, check history of assessments and download the recommendations in Excel or PDF.
This critical Oracle Cloud tool helps you to find your sensitive data and stay compliant with the regulations that affect the information stored in your Oracle database, either on-premises or in the cloud, whether in Oracle Public Cloud (OCI), or even in third-party cloud vendors, such as AWS EC2 and Microsoft Azure. Data Safe is included for no additional cost for OCI targets and with a monthly fee for non-OCI targets.
Why is it so important to protect sensitive data?
Sensitive data is information that you want to keep from being publicly available, because it is private and releasing it can lead to harm, such as identity theft, fauds, robs, business disruption, reputation risk and several other misuses, and therefore governments around the world have created mandatory regulations that may require your compliance depending on your business area. For example, the European Union General Data Protection Regulation (GDPR) enforcement since May 2018, the California Consumer Privacy Act of 2018 (CCPA), and over the last five years, many industry standards have been updated, including the International Organization for Standardization (ISO) 27701 in 2019.
Others such as the Payment Card Industry Data Security Standard (PCI DSS), detail specific controls that organizations must use while others apply generalizations that allow for customization. There are also specific area compliances like the Health Insurance Portability and Accountability Act (HIPAA), which covers entities that need to protect and secure patient’s healthcare data and Protect Health Information.
Despite the number and diversity of these laws, nearly all incorporate a similar set of requirements for protecting sensitive data.
Last but not least, industry reports say that one-third of attacks are performed by internal players (or “bad actors”) and half of those are on databases, so nowadays you should worry about who can see and change what into your environments, for both production and non-production.
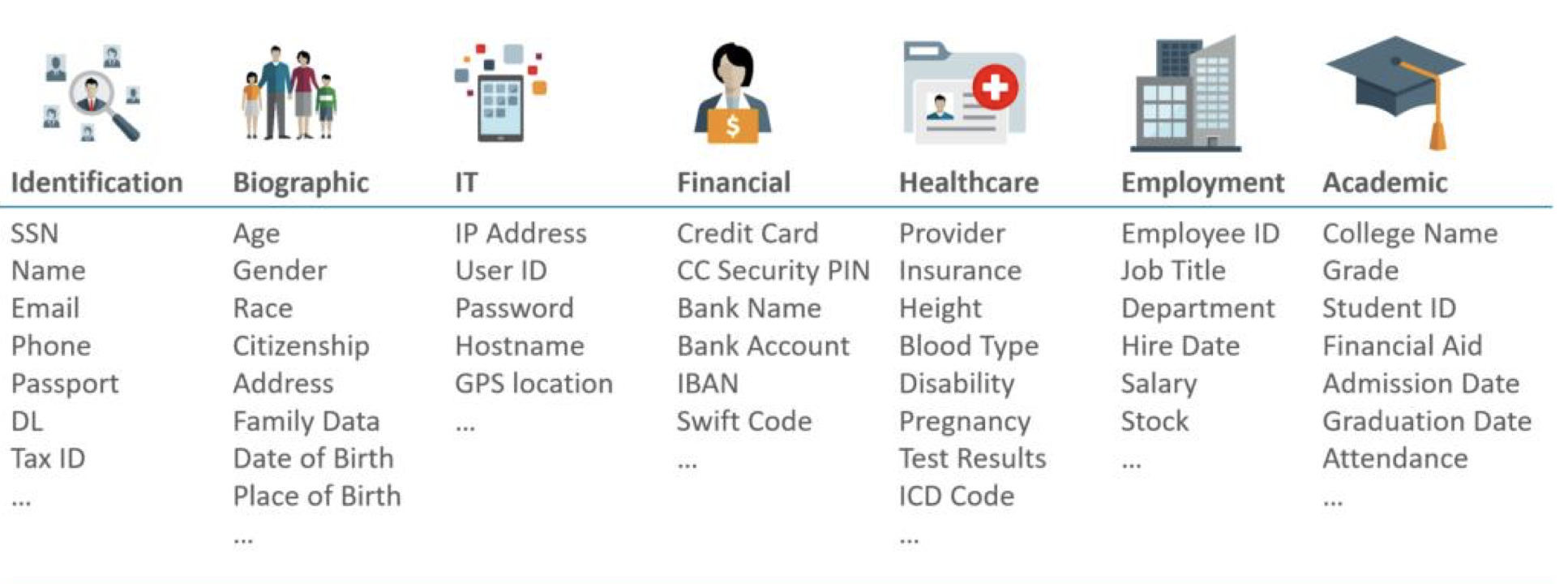
Sensitive Data categories examples:
Critical questions you need to consider
Security and user assessment
- Are your databases securely configured?
- Do you have any highly privileged accounts that could pose a risk to your database?
- Do you have gaps in your configuration strategy?
- How can you best remediate these gaps?
Sensitive data recovery
- What types of sensitive data do you have?
- How much sensitive data is stored in your database?
- Where is your sensitive data located?
Data protection
How can you efficiently support non-production environments and analytics without exposing sensitive data?
Audit
- How can you manage the audit data collected from individual servers?
- How can you centralize audit data to simplify reporting and event correlation?
- How can you be alerted to inappropriate user activity?
Automation
- How much time and effort do you need to invest to achieve all above items by doing manual work?
Now, consider Data Safe as the solution that resolves all above issues, helping you to assess, protect and improve your information security, with fast and reliable Service that will provide reports to you and, if desired, can also set audit rules with alerts and could also transform your environment’s real data in redacted or artificial data. This is very important for: non-production, performance testing, analytics and your life development cycle.

Follow 3 simple steps to start using Data Safe from your Oracle Cloud Infrastructure console
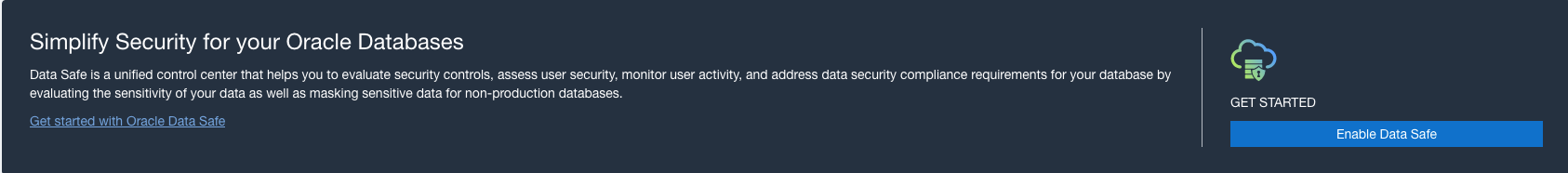
- From navigation menu, select Oracle Database, then click on Data Safe and you will see the button “Enable Data Safe”
- You must belong to your tenancy’s Administrators group or a defined group that has at least the “manage” permission for Oracle Data Safe and can “inspect groups” within the tenancy
2. The next screen you will see is to select the kind of target database you want to configure to be evaluated by Data Safe. The configuration process will be guided by a wizard, options are:
- Autonomous Database (ATP, ADW)
- Oracle Cloud Database (DB System: bare metal, virtual machine, Exadata)
- On-Premises Database (your non-cloud DB, this option has a cost)
- Compute Database (can be OCI or non-oracle cloud like AWS or Azure)
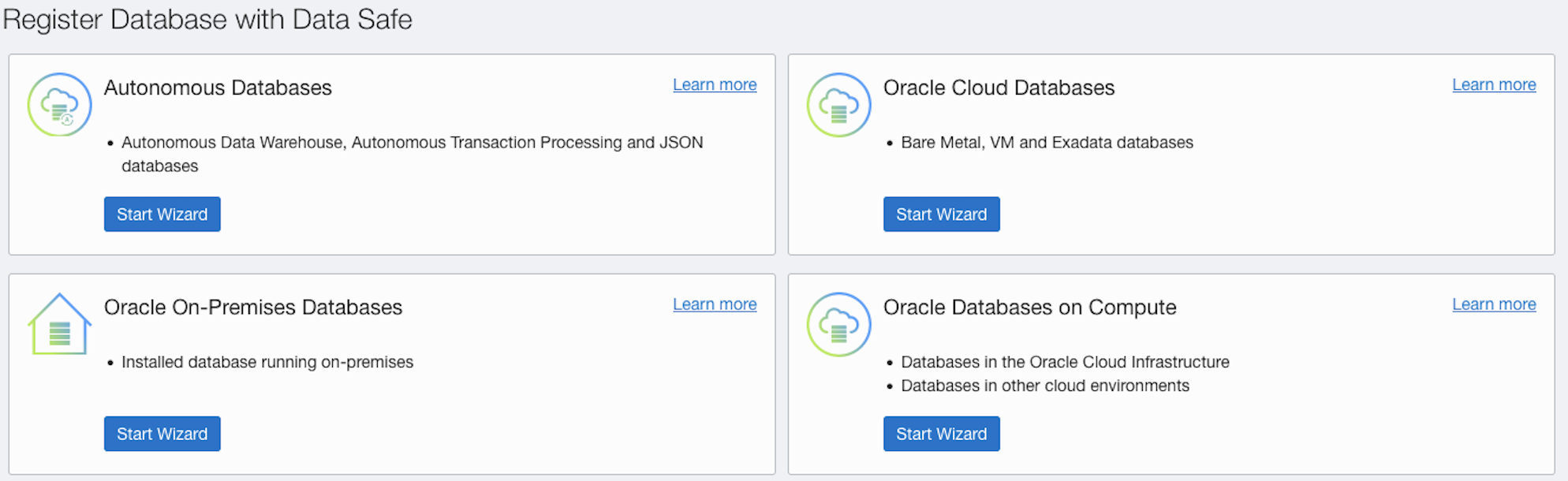
When registering your Targets using the Wizard, it will guide you to configure OCI connectivity for Data Safe to be able to read from your databases, you can use OCI Security Lists or OCI Network Security Groups, either option has to exist already before start the wizard, so you can select it to be used, the wizard will add the required ingress and egress rules for data safe to be able to communicate with target.
There are two important steps you must first perform in your database prior to completing the set up of Data Safe:
- Create a service account (user DataSafe_Admin with only minimal privileges like connect and resource) needed for Data Safe to connect and perform the queries required to extract its required metadata, user “DataSafe_Admin”. Do not use SYSTEM or SYSAUX as its default tablespace because you won’t be able to mask data.
- Grant the required roles using the script “datasafe_privileges.sql” (or if in Autonomous DB then run the package “DS_TARGET_UTIL.GRANT_ROLE”) – this script is provided by (and can be downloaded from) the OCI data safe registration wizard.
- (Optional) Only if you have Database Vault enabled and want to use the Data Masking Feature, then as the DV_Owner granted user authorize the ADMIN user to the “Oracle System” privilege and role “Management Real”, also connect as the ADMIN user and grant “Unlimited Tablespace” to the DS$ADMIN user.
After completing the register steps, Data Safe will automatically run the Security Assessments.
For more detailed information, refer to the “Administering Oracle Data Safe” manual:
https://docs.oracle.com/en/cloud/paas/data-safe/admds/administering-oracle-data-safe.pdf
For reference, the following is a summary of connectivity methods from Data Safe to the various different types of target databases:
| Oracle Database: | Connectivity Options: |
| Autonomous DB on shared Exadata Infrastructure | DB can have public or private IP, if DB has:
|
| Autonomous DB on dedicated Exadata Infrastructure | DB has private IP and connects via the Data Safe private endpoint. |
| DB System (DBCS) | Bare metal and VM DB systems can have public or private IPs – if the DB has:
Oracle Exadata Cloud Service DB can have private IP and connects via a Data Safe private endpoint |
| Compute Instance in OCI | DB has a private IP, can connect with Data Safe private endpoint (recommended) or with On-Premises “Connector” (which is another component based on Oracle Connection Manager [CMAN]) |
| Compute Instance in Non-Oracle Cloud | DB has a private IP, can connect with on-premises Connector (recommended) or with Data Safe private endpoint |
| On-Premises and Exadata Cloud at Customer | DB can have public or private IP, can connect using:
|
| Amazon RDS | Oracle AWS RDS databases are not supported (only AWS EC2 based databases, which fits as non-Oracle cloud DB) |
If your database has a public IP address or if it is accessible from the Internet through an internet Gateway, Data Safe refers to the IP as a “Public Endpoint”. If your database has a private IP address within a private subnet, then Data Safe refers to the IP as “Private Endpoint”. For this type of target, one of following connect resources is required (you don’t need to create a public IP address for your database):
- Oracle Data Safe Private Endpoint
- Oracle Data Safe On-Premises Connector
3. Once you finish the registration, the last step is to navigate to the Data Safe console and proceed to use its modules and take advantage of all its capabilities.
-
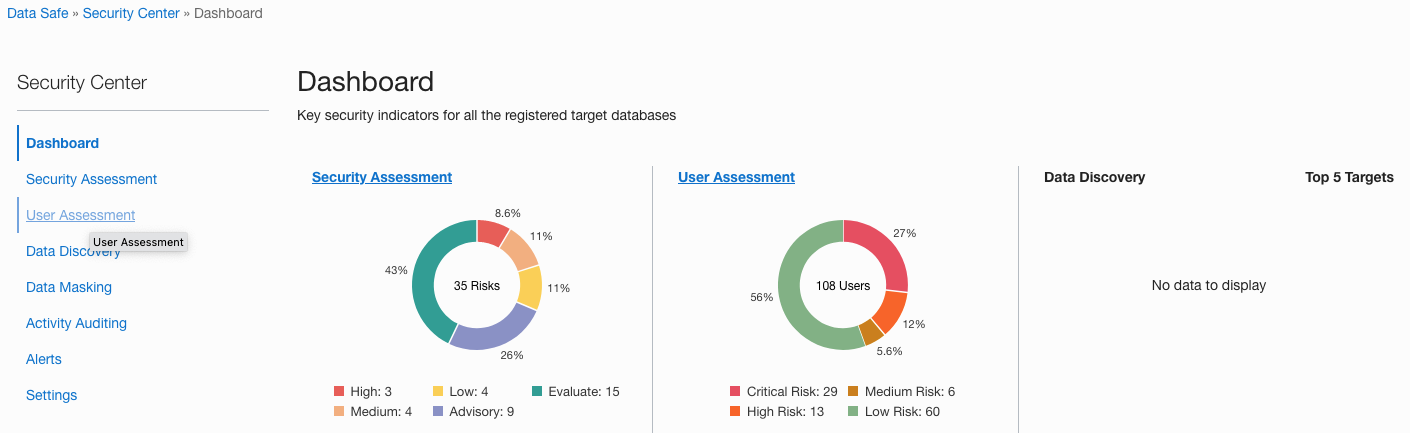
- Go to: Oracle Databases, then Data Safe and click on “Security Center”
Note:
If you’re a paid subscriber to any cloud database on OCI, you can use Data Safe at no additional cost for these databases.
You can store up to 1 million audit records per month per target database free of charge. If you exceed this limit, you may incur additional costs.
Oracle has built in some limits to prevent abuse, find more information here:
https://docs.oracle.com/en/cloud/paas/data-safe/udscs/service-limits.html
In the Security Center you will find:
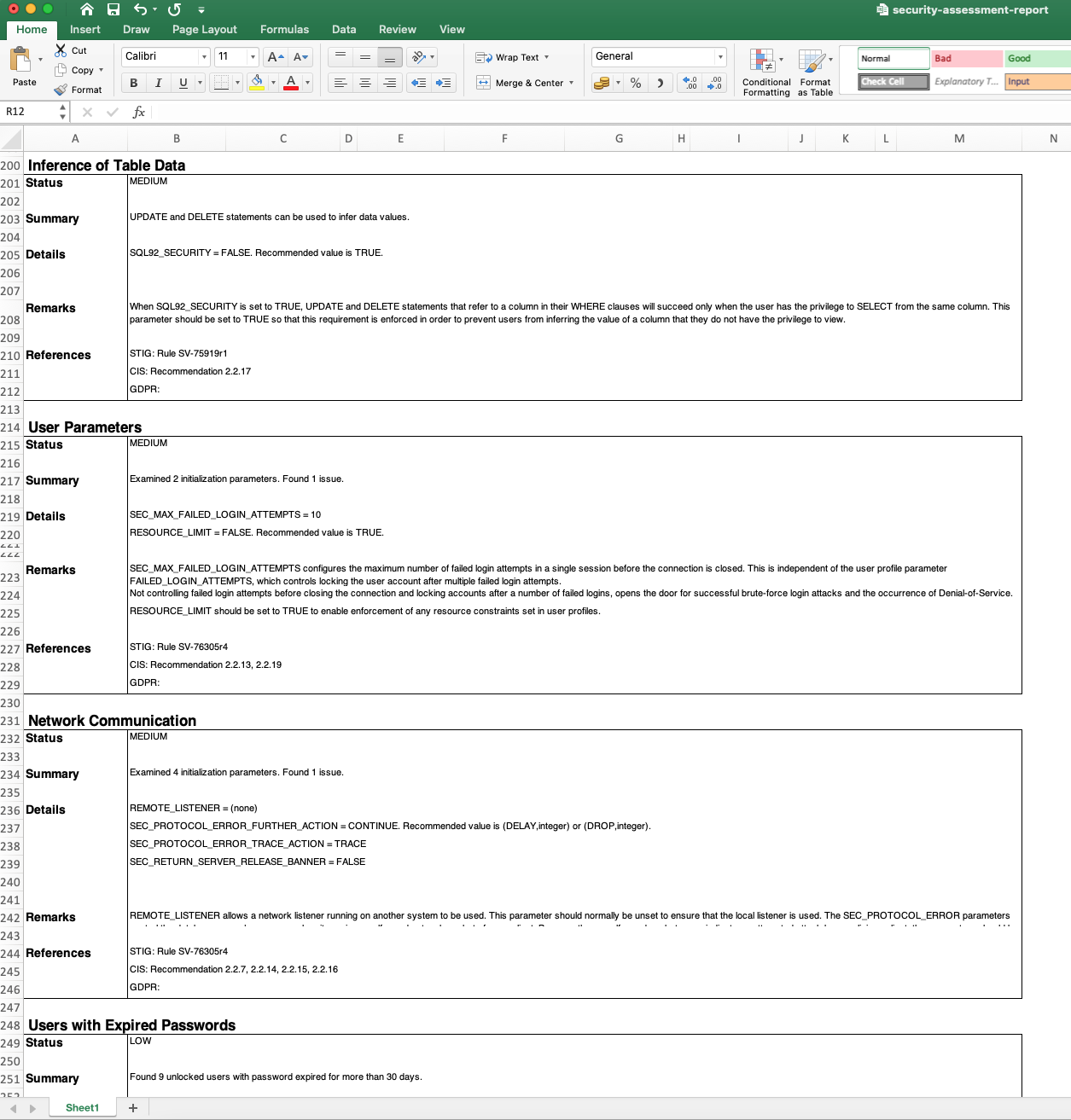
- Security assessment: This is an evaluation functionality that produces a report of your target database security, it shows several items categorized from “High Risk” to “Low” and “Evaluate” – it also provides a brief explanation of the risk and reference to which security standard or regulation corresponds to the recommendation.
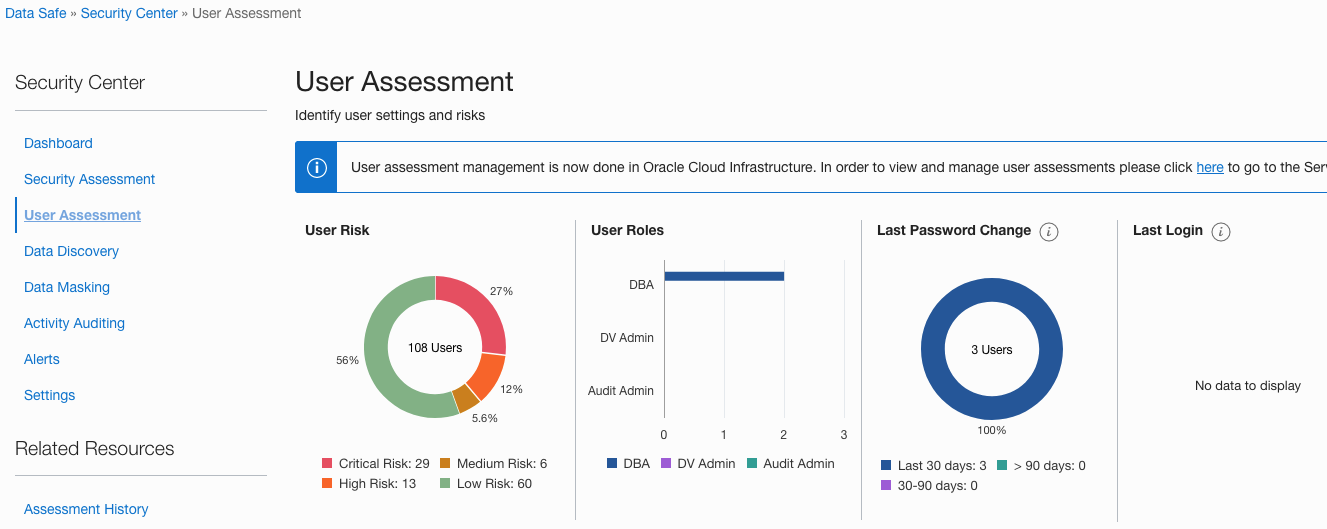
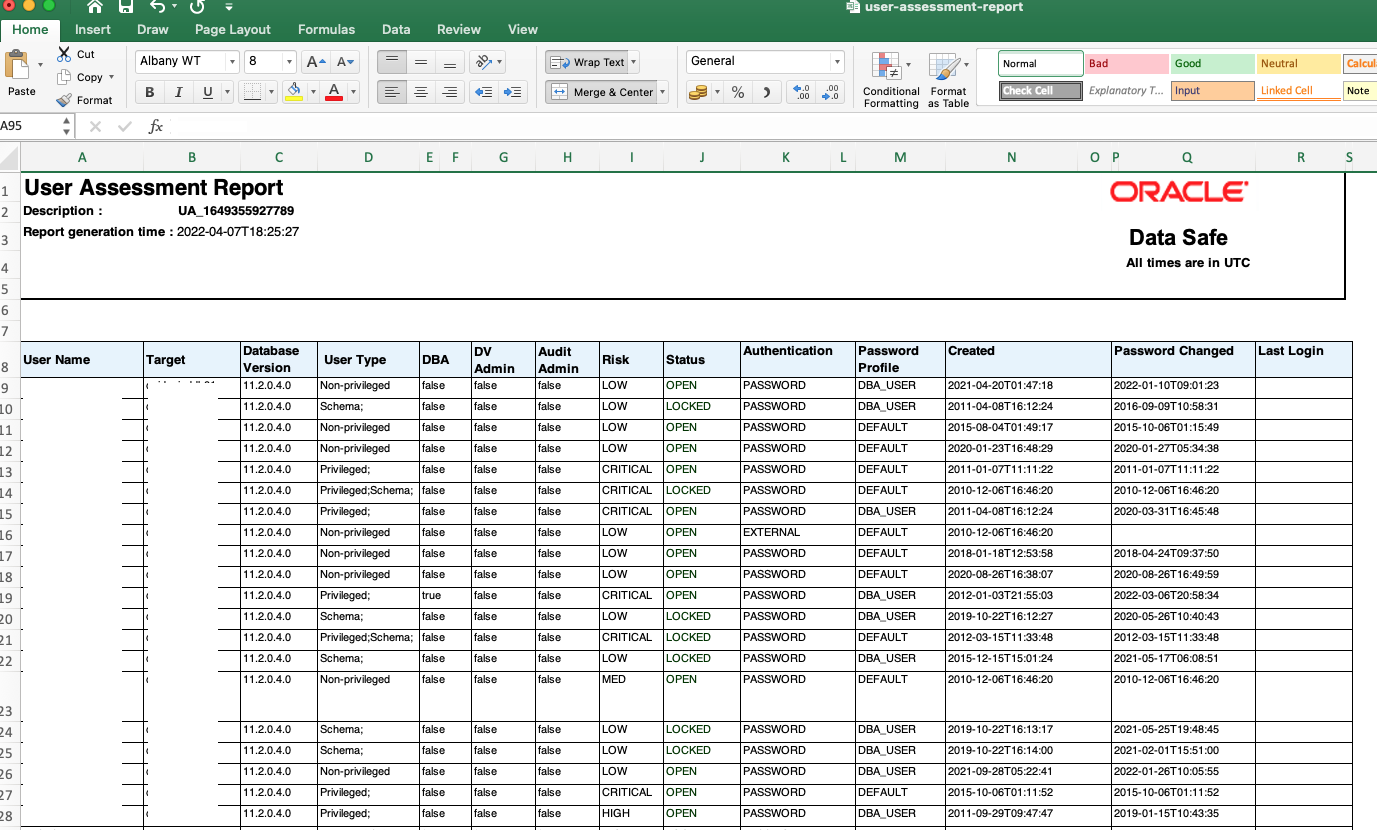
- User assessment: This is a report based on your target database users and schemas, categorizing risk based on the last time the password was changed, the last time user logged in, profile, account status, DB version and others.
- Data discovery: This is a module able to find potential Schemas, Tables and Columns which may contain Sensitive Data. It provides a detailed report of where the sensitive data was found so you can review and take any action if needed, for example either just review who can access those tables or add some auditing policy and or alert whenever users are accessing or changing such important data.
- Data masking: This module can work with the Sensitive Data model provided from Data Discovery and assist you to mask or change all that private data (for example in case of a non-production environment refreshed from Production, note that unlike an on-premises environment, for OCI targets no additional license or Advance Security option is required to use Data Masking feature).
- Activity auditing: Is the module to enable the auditing policies over your target database, note that provisioning and retrieval of audit policies is not supported for Databases with versions prior to 12.2. Configuration allows you to set alerts for events as you see fit.
- Alerts: This space shows the alerts produced based on the Activity Auditing module.
- Settings: Shows the default settings for Data Safe, including Global Paid Usage (if more than 1 million audit records is required, you can permit the additional charges, or you can disable and auditing will stop to avoid the additional costs). Audit data can be retained for forensic and compliance purposes, retention period can be from 1 to 12 months for online immediate availability audit reports or archived up to 82 months, which are not immediately available but can be retrieved back online if required.
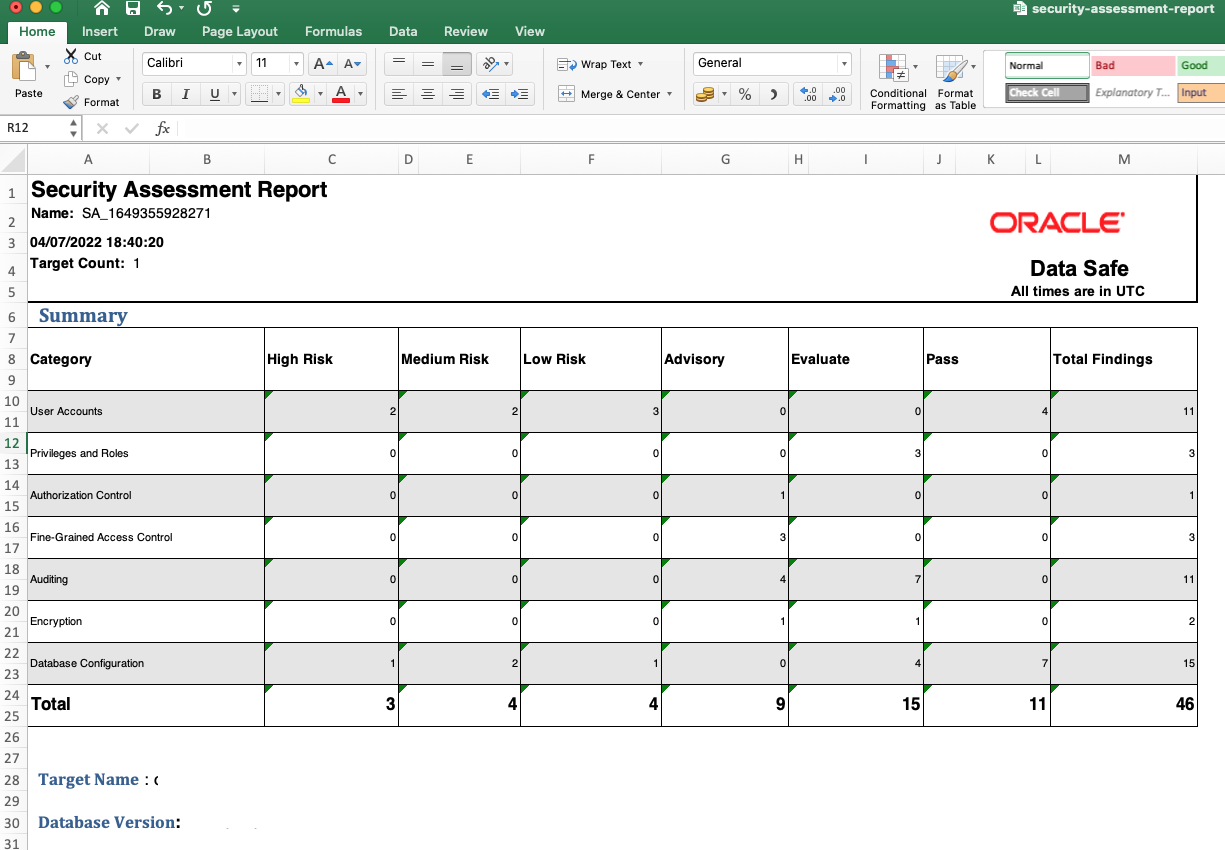
The following is a sample of a small part of the Security Assessment report for your reference (this is part of a report generated and downloaded in .xls format). This sample is from a Dev/Test environment:
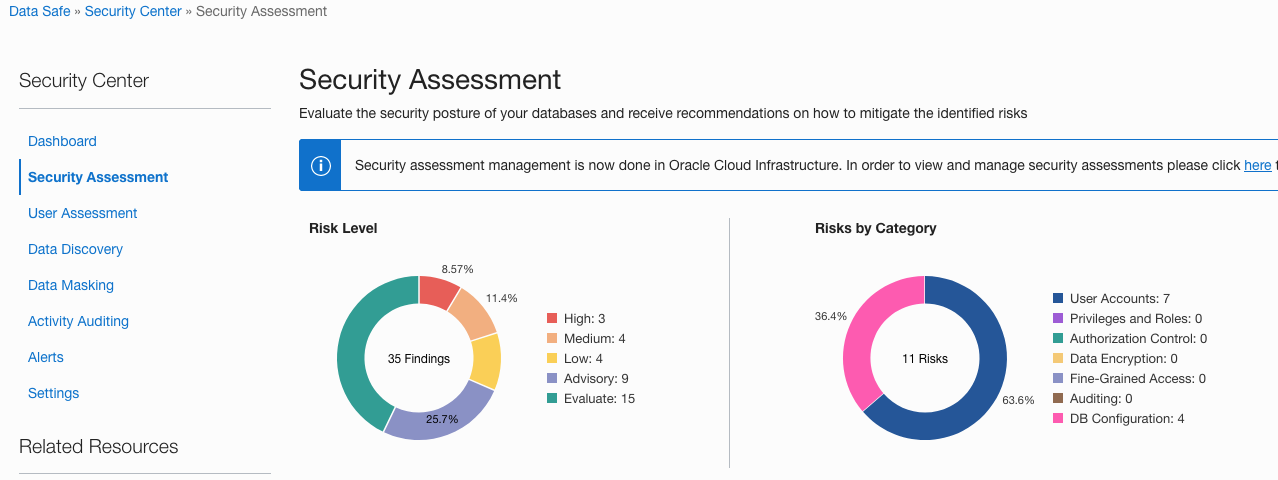
And the following sample shows a portion of Users Assessment output (with some information removed from the images)
Conclusions
- Oracle Data Safe is a powerful cloud tool that should be part of your data security strategy for all your Oracle databases. It can be extremely valuable for ensuring compliance with regulations.
- If you’re using it against OCI based targets , then you can run it completely for free.
- The cost to run it on on-premises (or against a 3rd party cloud database) is low compared to value provided and time and effort savings if the same work were to be performed manually.
- Data Safe setup and execution is very easy and automated in the OCI console.
- If still unsure to proceed to use Data Safe in your tenancy, give it a try for free using following link or QR code:
https://apexapps.oracle.com/pls/apex/dbpm/r/livelabs/view-workshop?wid=598

References:
https://www.oracle.com/a/tech/docs/dbsec/data-safe/faq-security-data-safe.pdf
https://www.cisecurity.org/benchmark/oracle_database
https://docs.oracle.com/en/cloud/paas/data-safe/books.html
https://www.oracle.com/security/database-security/what-is-data-security/
https://www.cpprotect.com/blog/what-is-sensitive-data/
https://blog.pythian.com/oracle-dbsat-discoverer-feature/
I hope this post useful. Let me know if you have any questions in the comments, and don’t forget to sign up for the next post.
Data warehouse services
Ready to migrate your data with confidence?
Share this
Share this
More resources
Learn more about Pythian by reading the following blogs and articles.

Oracle Cloud Infrastructure: Schemas in Oracle Autonomous Database

OCI Database Cloud Service Patching of Database and Grid Infrastructure Using OCI CLI
OCI Database Cloud Patching of Database & Infrastructure With CLI
Ready to unlock value from your data?
With Pythian, you can accomplish your data transformation goals and more.
